If you feel that someone is looking at you, maybe they are also listening. Because of the name “firefly. In this novel attack, careful observation of the power LED on the speaker allows the attacker to reproduce the sound being played. This is due to the almost imperceptible fluctuations in the brightness of the LED, which is most likely due to the sagging of the speaker’s power cord and recover.
You might think that if you can see the LED, you can hear the speaker output, but using a telescope through a window 100 feet away seems sufficient. You can imagine that you can use the same technique from a noisy office in the distance. We don’t know—but we suspect—even if the headset is plugged into the speaker, the LED will still modulate the audio. Any equipment that powers speakers is a potential source of leakage.
On the one hand, this is insidious because, unlike the more active forms of eavesdropping, it is almost impossible to detect. On the other hand, attacks also have various low-tech and high-tech mitigation measures. Low technical content? Close the blinds or cover the LED with tape. high tech? Enter a random frequency into the LED to destroy any leaked information. Super espionage technology? Place the fake speakers in front of the real speakers and they will silently play error messages on the LED.
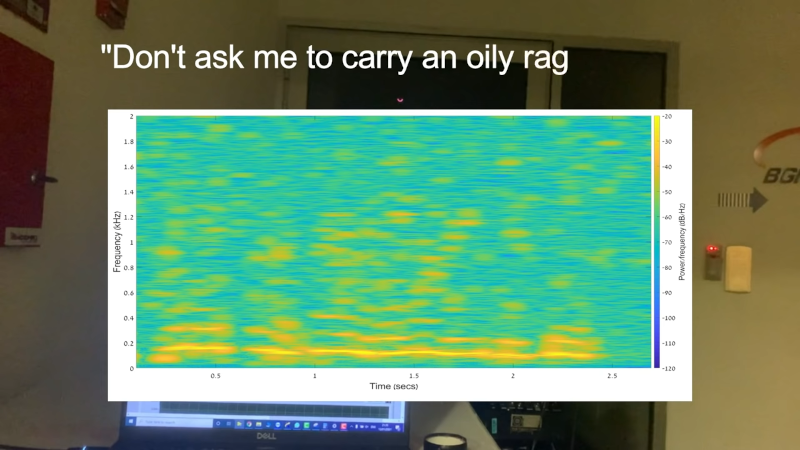
The video plays a sample of the restored voice. To be honest, it is clear enough but not very good. We want to know if some additional signal processing will help.
Passive errors are hard to find. Even a fancy connection detector will not tell you if your speakers are affected by fireflies.